If your business still uses NRIC numbers to authenticate customers, PDPC wants you to stop. And they're not asking nicely.
You Think You're Protecting Your Customers' Data. Here's the Irony — You're Not.
Date
Mar 13, 2026
Author
Steven Choong
𝗬𝗼𝘂 𝗧𝗵𝗶𝗻𝗸 𝗬𝗼𝘂'𝗿𝗲 𝗣𝗿𝗼𝘁𝗲𝗰𝘁𝗶𝗻𝗴 𝗬𝗼𝘂𝗿 𝗖𝘂𝘀𝘁𝗼𝗺𝗲𝗿𝘀' 𝗗𝗮𝘁𝗮. 𝗛𝗲𝗿𝗲'𝘀 𝘁𝗵𝗲 𝗜𝗿𝗼𝗻𝘆 — 𝗬𝗼𝘂'𝗿𝗲 𝗡𝗼𝘁.
𝙄𝙛 𝙮𝙤𝙪𝙧 𝙗𝙪𝙨𝙞𝙣𝙚𝙨𝙨 𝙨𝙩𝙞𝙡𝙡 𝙪𝙨𝙚𝙨 𝙉𝙍𝙄𝘾 𝙣𝙪𝙢𝙗𝙚𝙧𝙨 𝙩𝙤 𝙖𝙪𝙩𝙝𝙚𝙣𝙩𝙞𝙘𝙖𝙩𝙚 𝙘𝙪𝙨𝙩𝙤𝙢𝙚𝙧𝙨, 𝙋𝘿𝙋𝘾 𝙬𝙖𝙣𝙩𝙨 𝙮𝙤𝙪 𝙩𝙤 𝙨𝙩𝙤𝙥. 𝘼𝙣𝙙 𝙩𝙝𝙚𝙮'𝙧𝙚 𝙣𝙤𝙩 𝙖𝙨𝙠𝙞𝙣𝙜 𝙣𝙞𝙘𝙚𝙡𝙮.
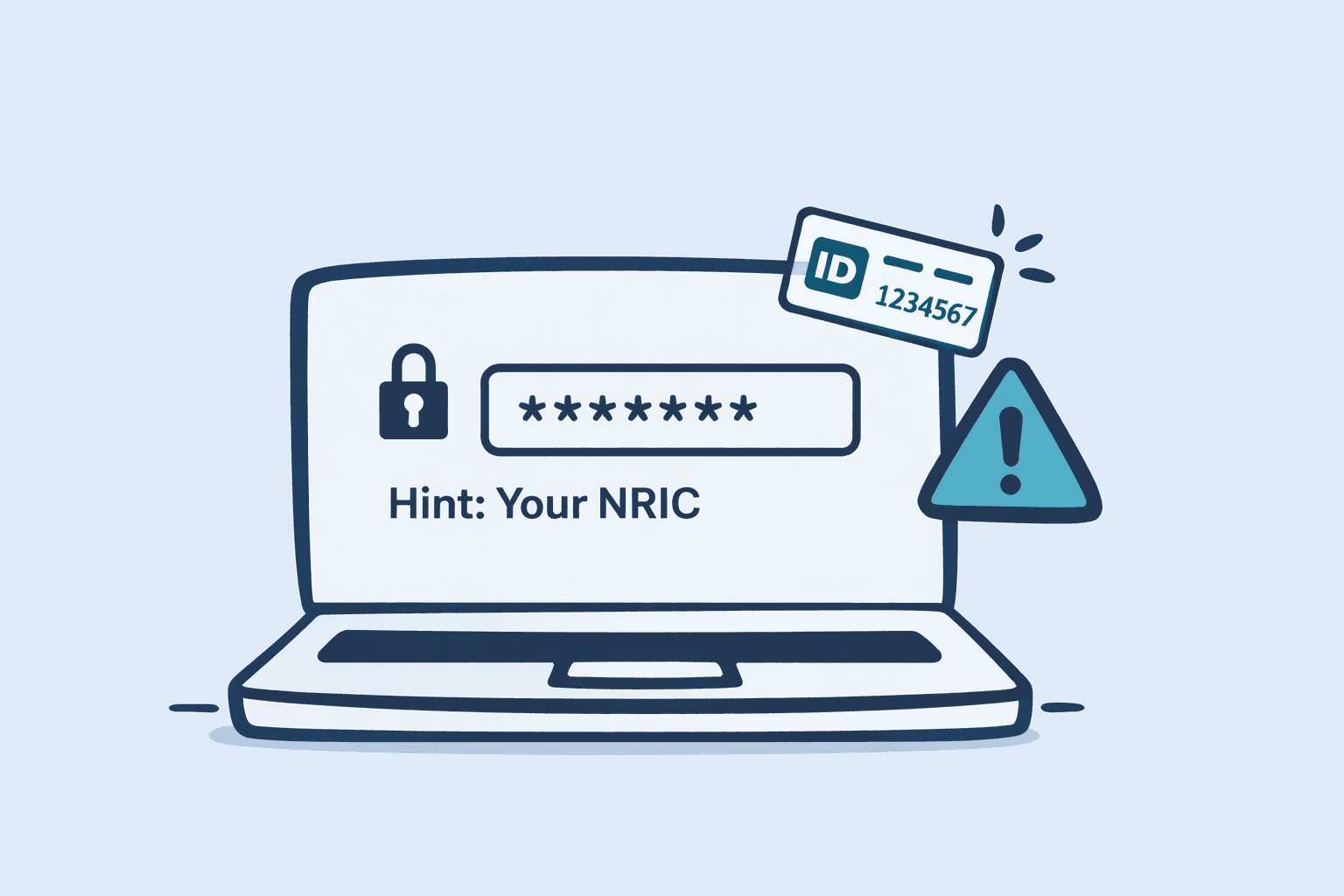
You send your customer a PDF statement. Before they can open it, you ask them to key in the last four digits of their NRIC. Feels responsible, right? You're verifying their identity. You're protecting their data.
Except you're not. You're doing the opposite.
Every time you ask a customer to key in their NRIC — full or partial — to access a file, open an account, or verify their identity, you're asking them to risk one piece of confidential data in order to protect another. That's not security. That's a paradox.
PDPC has recognised this, and they've made it clear: businesses should not use full or partial NRIC numbers as an authentication factor. This isn't a suggestion. Enforcement begins by January 2027, and if your systems still rely on NRIC-based authentication by then, you are not compliant with the PDPA.
𝗪𝗵𝗮𝘁 𝗧𝗵𝗶𝘀 𝗠𝗲𝗮𝗻𝘀 𝗳𝗼𝗿 𝗬𝗼𝘂𝗿 𝗕𝘂𝘀𝗶𝗻𝗲𝘀𝘀
If you currently use NRIC — even just the last four digits — for any of the following, you need to make changes:
Password-protecting PDF statements or documents
Customer login or account verification
Identity authentication for accessing sensitive information
The intent behind the guideline is straightforward: NRIC numbers are permanent, unique identifiers. They cannot be changed if compromised. Using them as passwords or PINs treats them as disposable credentials when they are anything but.
𝗠𝘆 𝗔𝗱𝘃𝗶𝗰𝗲 𝗮𝘀 𝗮 𝗗𝗣𝗢
𝗙𝗶𝗿𝘀𝘁, 𝗮𝘂𝗱𝗶𝘁 𝘆𝗼𝘂𝗿 𝘀𝘆𝘀𝘁𝗲𝗺𝘀 𝗻𝗼𝘄. Identify everywhere your business uses NRIC — full or partial — for authentication. Don't wait until late 2026 to scramble.
𝗦𝗲𝗰𝗼𝗻𝗱, 𝘀𝘄𝗶𝘁𝗰𝗵 𝘁𝗼 𝗽𝗿𝗼𝗽𝗲𝗿 𝗮𝘂𝘁𝗵𝗲𝗻𝘁𝗶𝗰𝗮𝘁𝗶𝗼𝗻 𝗺𝗲𝘁𝗵𝗼𝗱𝘀. There are proven alternatives that protect your customers without putting their personal data at risk:
SMS or email one-time passwords (OTP)
Two-factor authentication (2FA) apps
Unique PINs or passwords set by the customer themselves
𝗧𝗵𝗶𝗿𝗱, 𝘀𝘁𝗼𝗽 𝘂𝘀𝗶𝗻𝗴 𝗯𝗶𝗿𝘁𝗵 𝗱𝗮𝘁𝗲𝘀 𝘁𝗼𝗼. PDPC hasn't explicitly banned birth dates as authentication yet, but as a DPO, I'd tell you it's only a matter of time. Birth dates are easily guessable and widely exposed. Don't replace one soon-to-be-banned method with another that's heading in the same direction.
𝗗𝗼𝗻'𝘁 𝗪𝗮𝗶𝘁 𝗳𝗼𝗿 𝗘𝗻𝗳𝗼𝗿𝗰𝗲𝗺𝗲𝗻𝘁 𝘁𝗼 𝗙𝗼𝗿𝗰𝗲 𝗬𝗼𝘂𝗿 𝗛𝗮𝗻𝗱
You have until January 2027. That sounds like plenty of time — until you factor in system changes, vendor coordination, and customer communication. Start now.
If you need help auditing your authentication practices or transitioning to compliant alternatives, schedule a consultation with us at Veritos - https://calendly.com/veritos/introductory. We'll help you get this sorted before the deadline, not after.
PDPC’s official announcement can be found in their press release:
Organisations to Cease the Use of NRIC Numbers for Authentication by 31 December 2026
https://www.pdpc.gov.sg/news-and-events/press-room/2026/01/organisations-to-cease-the-use-of-nric-numbers-for-authentication-by-31–december-2026
